Views: 1764

Future war “may see attacks via computer viruses, worms, logic bombs, and trojan horses rather than bullets, bombs, and missiles”
[Steven Metz, Armed Conflict in the 21st Century: The Information Revolution and Post-Modern Warfare, Carlisle, PA: Strategic Studies Institute, 2000, xiii].
First part
The facilities of the Internet in politics
The Internet or the WWW (World Wide Web) became massively widespread around the globe since the late 1980s or more precisely since 1989 – in the same year when the Berlin Wall collapsed and, therefore, enabled the Cold War 1.0 to enter the final stage of its end. That is why both of these historical events mark the start of the Turbo-Globalization Era in all spheres from economy to culture including politics as well.[i] With the growing importance of the Internet, it is quite understandable that it is becoming an arena of political and ideological rivalry with necessary growing implications concerning national security issues.[ii]
The spread of mass media via the Internet followed by the communications within the framework of cyber-space[iii] enable ever more people, even in remote corners of the globe, to be informed (or misinformed) about the world affairs, form (or to accept) opinions about certain events, and to be involved in politics in ways that some 30−35 years ago have been unimaginable. Today, even poor peasants in many parts of the world have access to the Internet that provide information and give both Government’s and anti-Government’s groups new way to struggle for their ideas, ideologies, and programs in order to indoctrinate publics.
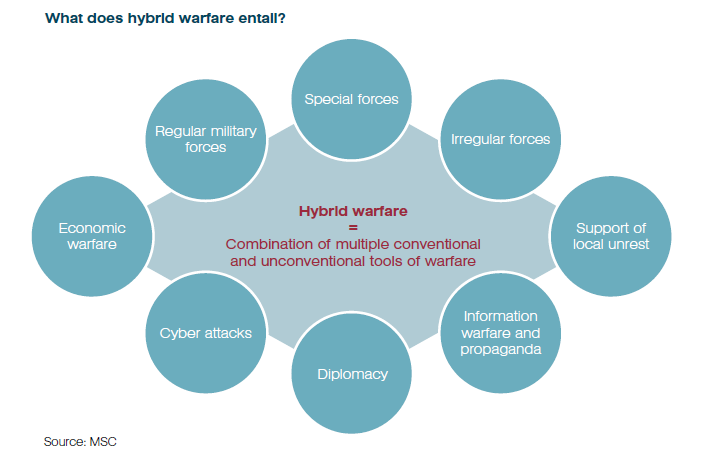
The Internet already became the focal instrument of all in facilitating the exchange of different viewpoints, dissemination of information, fake news or propaganda, movement of electronic money, and finally the coordination of activities for the obvious reason as it is inexpensive and easily accessible. The bloggers with their weblogs are influencing mass of people across the globe by transmitting both information and disinformation and opinion on the Internet.[iv] After the end of the Cold War 1.0, a new Cold War 2.0 started in which the Great Powers started to adopt smart weapons to fight conventional wars, weapons that utilize new information and communication technologies like the Internet or cyber-space. A new type of warfare emerged – cyber-war.[v]
What concerns the politics, the focal impact of the Internet on it can be summarized into four basic points:
- The real technical possibility of the Internet to increase and improve the transparency of the Government by free access to online content, official documents, and all kinds of governmental reports and viewpoints on different issues and problems.
- The ability of the Internet to increase the politically relevant set of information of both natures factual and hoax.
- Its power to organize and speed up the coordination of different interest groups, extremist groups, and the so-called civil society beyond something that was known before as traditional political areas and barriers.
- The creation of new forms of criminal activities known as cyber-crime, cyber-terrorism, or cyber-security problems.
In regard with the first point of the possibility to increase transparency, Governments, the NGOs, and different institutions in global governance (like the OUN) have created several millions of Web-pages for the purpose to offer political information as official reports, viewpoints, comments, contact forums or strategy rationalizations. Many Governments, established increasing targets for the maximum proportion of their communication with the citizens via the Internet.
Nevertheless, if we are speaking about information flows, the Internet is offering for sure a cheap and easy platform for many types of populist movements, parties, or organizations seeking to indoctrinate and attract a possible voting audience at the elections.[vi] One such very successful examples, as a matter of illustration, was by the US Democrats in the presidential election of Barack Obama in 2008.
The facility of the Internet allows for greater communication of identity politics like, for instance, those witnessed during the British referendum to leave the EU – the Brexit.[vii] However, another facility that the Internet offers in practice is the spreading of propaganda[viii] by extremist persons or organizations for most different purposes. One of such most blatant recent examples of misusing of the Internet facilities for the very political and/or ideological purposes is used by the ISIS[ix] and other Islamic fundamentalist or radical groups[x] for the recruitment strategies.
The Internet in general and social media in particular as well as provide powerful platforms for the greater dissemination of the so-called fake news. Such news is a form of uncorroborated media is popularized by many of online views generated, rather than from traditional forms of independent channels of verification. Concerning the former, many experts would argue that both the promotion of fake-news and targeted viewer profiling on the Internet (particularly on Twitter) tremendously participated in the election of Donald Trump for US President in November 2016.
One of the crucial power features of cyber-space is that it poses real challenges to Governments as the Internet facilitates mobilization and coordination by professionals, freedom fighters, insurgents, criminals, and terrorists of all kinds. As a good example of the using Internet against authoritarian regimes can be the case of WikiLeaks in April 2010 when a video that showed a US helicopter in Baghdad killing a dozen Iraqis including two journalists appeared on the net.
Cyber-crime
Cyber-crime, in essence, refers to traditional types of crimes that just migrated to cyberspace (the Internet), such as money laundering or sexual exploitation. However, the cyber-crime as well as include the internet specific criminal activities like illegal access to electronic information, trade, national or political secrets, and finally the creation and spread of dangerous computer viruses which can impose political or national-security harmfulness.
Cyber-crime committed by individuals or state-sponsored cyber-attacks undoubtedly are posing serious threats to the international community in general or a particular part of it for the very reason they are in principle designed to degrade, deny or even destroy information resident in computers or to compromise computers themselves. Such activities of cyber-attacks or cyber-terrorism are committed with the ultimate task to inflict disruption, destruction, or human loss.
Cyber-crime can be a foremost threat to individuals, industry, or/and political organizations as well as. But in political terms, the cyber-crime can question the proper function of the state and its political system if the latter persistently fails to control such criminal activity or if it suffering breakdowns in cyber-security.
One of the very specific types of cyber-crime is cyber-terrorism. It basically refers to the (mis)use of the Internet facilities by different organizations to promote terrorist propaganda and activities. The terrorist groups can use the Internet as a domain to commit cyber-attacks by, for example, targeting networks or computers which belong to the governmental, public, or military infrastructures. The most notorious up to now cyber-program used in cyber-crimes is the so-called trojan horse – program in which a code is contained inside a program or data so that it can take control of a computer for the sake to damage it. However, an additional danger can be posed by computer trap doors or back doors – deliberate holes in computer programs that are used to gain unauthorized access to a computer or a computer network for the reasons to spy or/and cause destruction of the computer system.[xi]
However, the Internet as well as can be (mis)used to perpetrate acts of terror that produce physical or mental damage but in extreme cases, cyber-terrorists can incur individual criminal responsibility under international criminal law where their conduct is understood as supporting war crime, aggression, crimes against humanity, or genocide. In war terminology, cyber-war is the use of the system of information for the purpose to exploit, disrupt, or destroy an enemy’s military or civilian computer networks with the ultimate aim of disrupting those systems and the tasks they perform.[xii] Cyber-war is war in cyber-space that is already a new fifth military domain after land, sea, air, and space.
[i] Michael Meyer, The Year that Changed the World: The Untold Story Behind the Fall of the Berlin Wall, New York: Scribner, 2009; Brian McCullough, How the Internet happened: From Netscape to the iPhone, New York−London: Liveright Publishing Corporation, 2018.
[ii] See more in [John Erikkson, Giampiero Giacomello, “The Information Revolution, Security, and International Relations: (IR) Relevant Theory?”, International Political Science Review, 27/3, 2006, 221−224].
[iii] Cyber-space is “electronic medium of computer networks in which online communication takes place” [Richard W. Mansbach, Kirsten L. Taylor, Introduction to Global Politics, Second Edition, London−New York: Routledge Taylor & Francis Group, 2012, 575].
[iv] Daniel W. Drezner, Henry Farrell, “Web of Influence”, Foreign Policy, 145, 2004, 32−40.
[v] About cyber-war, see more in [Richard A. Clarke, Robert Knake, Cyber War, New York: HarperCollins, 2010]. This book is giving a picture of cyber-war and its capabilities which afford potential enemies.
[vi] See, for instance [Pipa Norris, Ronald Inglehart, Cultural Backlash: Trump, Brexit, and Authoritarian Populism, Cambridge, UK: Cambridge University Press, 2019].
[vii] The Brexit is abbreviated term by the British, meaning literary shorthand for the British leaving of the European Union. The Brexit refers to the debates in the direct connections with June 23rd, 2016 referendum for the UK to exit the EU. The Brexit referendum became a debate between two camps in the UK – those for the British leaving the EU vs. those for the British standing in the EU. About the Brexit issue, see more in [Harold D. Clarke, Matthew Goodwin, Paul Whiteley, Brexit: Why Britain Voted to Leave the European Union, Cambridge, UK: Cambridge University Press, 2017].
[viii] The term propaganda is historically originating in an office of the Roman Catholic Church in the Vatican charged with the propagation of the (Roman Catholic) faith – de propaganda fide. The term propaganda entered common usage in the 1930s in order to describe at that time the authoritarian regimes to achieve total subordination of knowledge to the policy of the state. Based on the politics of different kinds of authoritarian and totalitarian political regimes in Europe to develop legitimacy and social control by the centralized governmental institutions, propaganda soon came to be directed toward the populations of other states (usually the neighbours), provoking reactions from the other states. Therefore, for instance, the UK established the Ministry of Information. Such ministries employed print, radio, film, graphic art, and the oral word in order to justify the official policy of their Governments (the White Propaganda) but at the same time to beat the enemy’s propaganda (the Black Propaganda). Propaganda was quite important in the international relations during the Cold War 1.0 especially via radio stations like Radio Free Europe or Voice of America which have been propagating the official values of the Western political liberal democracy and market economy. Today, the Western political propaganda either via the Internet or other technical means is mainly directed against Russia and China in the forms of (extreme) Russophobia and Sinophobia. See more about propaganda in [Jason Stanley, How Propaganda Works, Princeton, US−Oxford, UK: Princeton University Press, 2015].
[ix] The ISIS (the Islamic State of Iraq and Syria) is an international terrorist organization based in both Iraq and Syria. The organization is known as well as the Islamic State of Iraq and the Levant (the ISIL) and as the Daesh (the Da’esh). See more in [Gus Martin, Understanding Terrorism: Challenges, Perspectives, and Issues, Thousand Oaks, California: SAGE, 2017; William McCants, The ISIS Apocalypse: The History, Strategy, and Doomsday Vision of the Islamic State, New York: St. Martin’s Press, 2015].
[x] The term Islamic fundamentalism or as a synonym Islamism is used in the West (especially in the USA and the UK) to mark any movement or organization which is favouring strict respect for the teaching of both the Qur’an and the Shari’a that is the Islamic Law.
[xi] See in more detail in [Jonathan Kirshner (ed.), Globalization and National Security, New York: Routledge, 2006].
[xii] Richard W. Mansbach, Kirsten L. Taylor, Introduction to Global Politics, Second Edition, London−New York: Routledge Taylor & Francis Group, 2012, 575.
Second part
The legal measures against cyber-crime
During the last decade or so, cyber-crime of all types is increasingly understood to be war-like attacks on states and their infrastructure and, therefore, are regulated mostly by the international legal framework relating to the use of force or, in the case committed at the time of war (armed conflict), by international humanitarian law.
All countries, or groups of countries, which are considered to belong to the Great Powers bloc implemented certain legal and practical measures to counter the cyber-crime on their authorized territory. One of the best successful examples so far is the Council of Europe which adopted the Convention on Cyber-crime in 2001 and 2004 by which established a common criminal policy among the Member States by both adopting appropriate legislative framework and encouraging transnational cooperation on the global level in the practice of beating cyber-crime in all spheres including the politics as well as. If we can speak in more precise legal terms, according to the legal framework of the European Council concerning beating cyber-crime, the Member States should criminalize illegal access, illegal interference, and at the same time, the Member States should cooperate by all possible legal and practical means in their examination and prosecution policies.[i]
It is clear decision by the OUN that such cyber-activities are undermining the global or regional peace process and security and, therefore, the organization called all its Member States to prohibit incitement to commit terrorism, take as possible as active measures for the sake to prevent incitement and deny safe haven to persons or group of persons who are guilty of incitement. Nevertheless, it is clear that any kind of adopted cyber-security measure must comply with the protection of international standards of human rights like the freedom of speech and association or the right to privacy.
As a matter of fact, within the legal framework of international agreements aimed for the suppression of terrorism in general, and more particularly on the Internet, states are subject to many international legal obligations that require their struggle against cyber-terrorism within the Internet space that is controlled by them. It is, for instance, the case of the UNSC which adopted several resolutions by which all the UN Member States are required to act against terrorist activities within their borders including cyber-terrorism too.
Endnotes:
[i] See more in [Robert W. Taylor, et al, Cyber Crime and Cyber Terrorism, Pearson, 2018].
 Prof. Dr. Vladislav B. Sotirović
Prof. Dr. Vladislav B. Sotirović
www.global-politics.eu/sotirovic
sotirovic@global-politics.eu
© Vladislav B. Sotirović 2020
Origins of images: Facebook, Twitter, Wikimedia, Wikipedia, Flickr, Google, Imageinjection, Public Domain & Pinterest.
Read our Disclaimer/Legal Statement!
Donate to Support Us
We would like to ask you to consider a small donation to help our team keep working. We accept no advertising and rely only on you, our readers, to keep us digging the truth on history, global politics and international relations.
[wpedon id=”4696″ align=”left”]
FOLLOW US ON OUR SOCIAL PLATFORMS